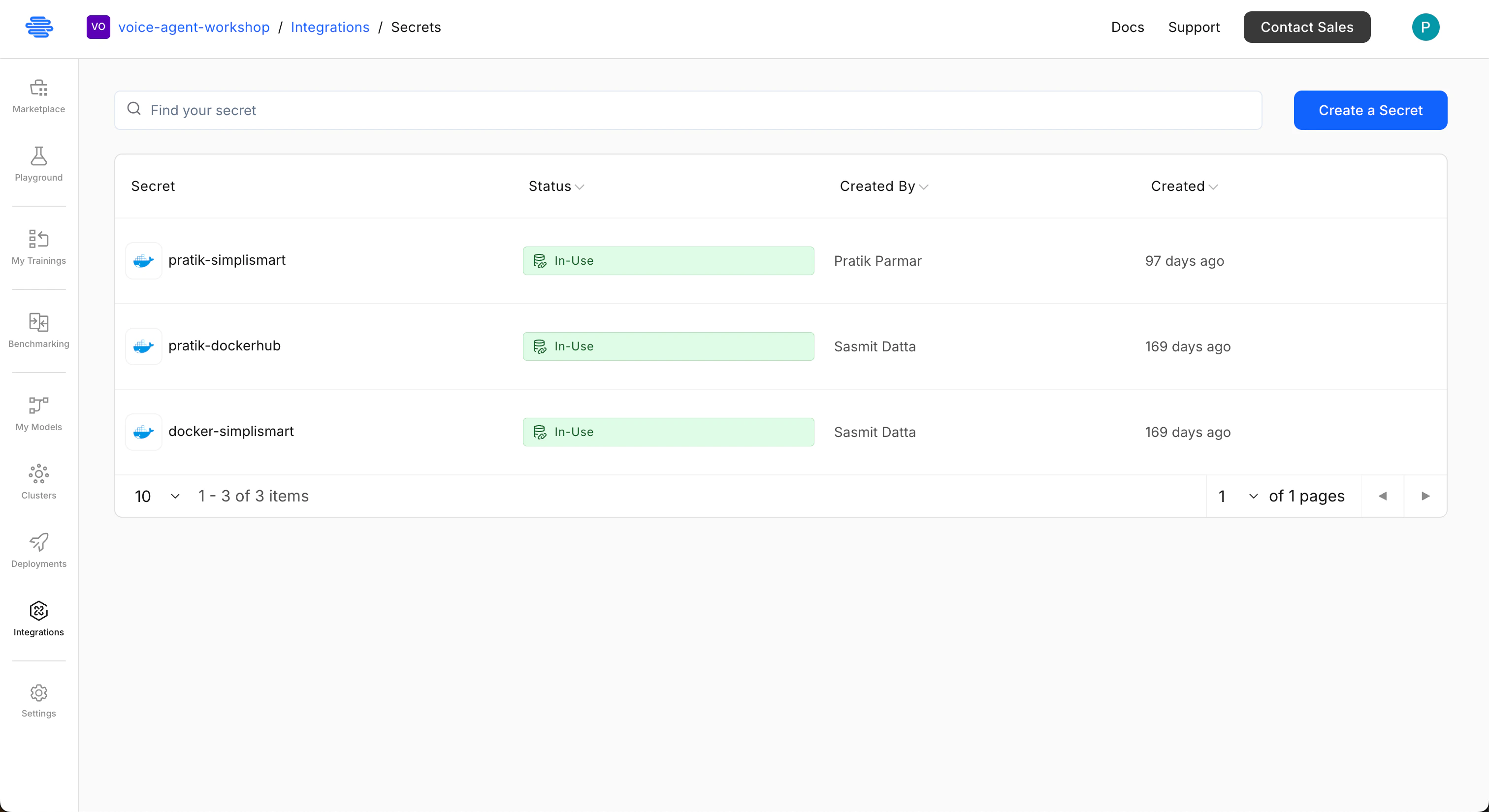
Secrets are secure credentials stored within Simplismart platform that allow the platform to access external systems such as cloud accounts, container registries, model sources, or Kubernetes clusters. Secrets typically include:Documentation Index
Fetch the complete documentation index at: https://docs.simplismart.ai/llms.txt
Use this file to discover all available pages before exploring further.
- Access keys
- API tokens
- Service account credentials
- Cluster authentication details
Why secrets are used
Secrets are required to:- Access cloud infrastructure for cluster creation or import
- Pull containers from private registries
- Download models from external sources
- Authenticate with Kubernetes clusters
- Credentials are not exposed in plain text
- Access can be centrally managed
- Integrations can be reused across deployments
Add a Secret
Define Secret Details
Enter a descriptive secret name and choose the appropriate secret type from the dropdown menu (e.g., 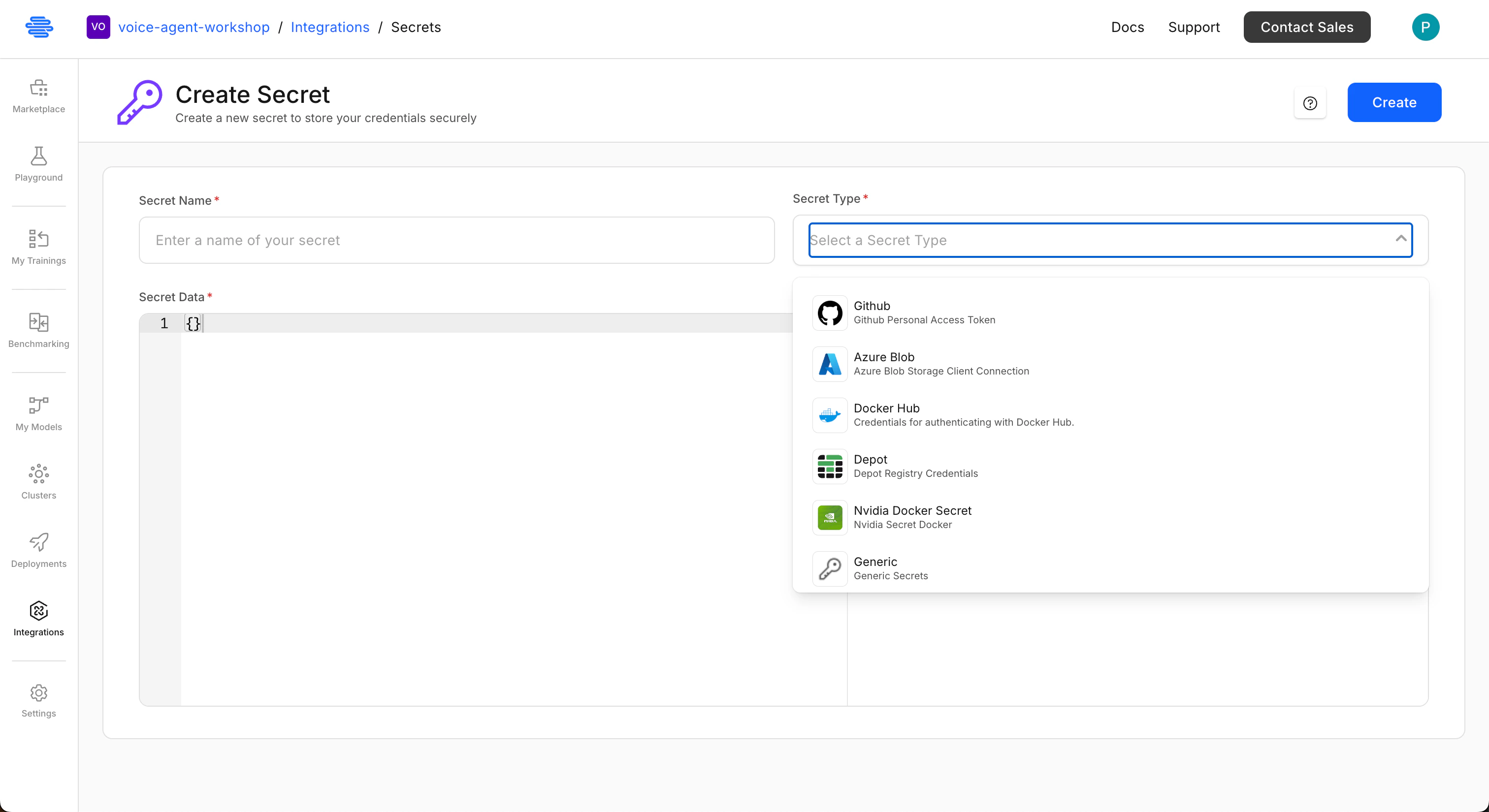
AWS, GCP, Docker Hub, Hugging Face, Kubernetes, Generic).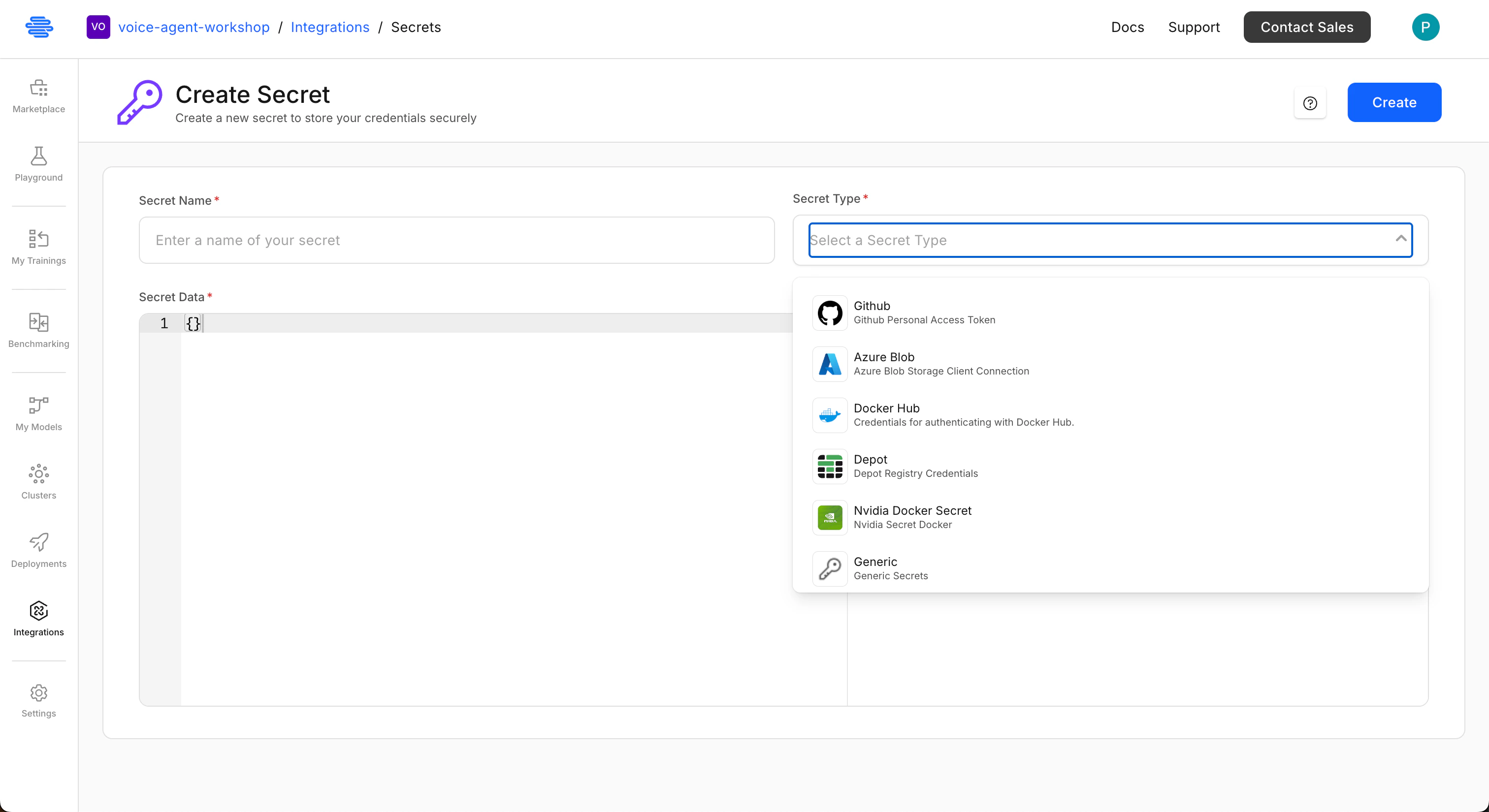
Input Credentials
Paste the credentials in the specified JSON format into the provided text area. Refer to the sections below for examples of required structures for each secret type.
Using Secrets
Secrets can be used in:- Cloud account integrations
- Cluster creation or import
- Container registry access
- Model source authentication
Edit Secrets
To modify an existing secret:Select and Edit
Locate the secret you wish to modify from the list, then click the Edit button on the top right corner of the screen.

Update Credentials
Adjust the credentials in the JSON format as needed. Ensure the new credentials are valid for the secret type.
Cloud Credentials
Cloud credentials (often referred to as cloud secrets) enable Simplismart to interact with your cloud infrastructure for tasks such as:- Creating or importing Kubernetes clusters
- Managing storage resources for model artifacts and training data
- Deploying workloads to your cloud environment
Use Dedicated Accounts
Allocate a dedicated cloud account, project, or subscription specifically for Simplismart operations to isolate resources and permissions.
Apply Least Privilege
Grant only the minimum necessary permissions required for Simplismart to perform its functions. Avoid overly broad access.
Rotate Credentials Regularly
Implement a policy for periodic rotation of access keys and API tokens to reduce the risk of compromise.
Avoid Root Credentials
Never use personal or root account credentials. Always use service accounts or roles with specific, limited permissions.
The specific permissions required depend on the actions Simplismart will perform (e.g., cluster creation vs. ongoing maintenance). For initial setup, broader access might simplify configuration, which can then be refined to a more restrictive policy.
Required Permissions for Cloud Providers
Below are the recommended initial roles for integrating with major cloud providers. These roles provide sufficient permissions for Simplismart to manage resources effectively. You can refine these permissions after the initial setup.- AWS
- GCP
- Azure
- QBlocks
AWS secrets allow Simplismart to create or manage EKS clusters and access storage resources.
Required Credentials
Provide the following fields in the JSON format:access_key_idsecret_access_key
IAM Policies
- S3 Access: Required for model storage, logs, and artifacts. Permissions:
s3:ListBucket,s3:GetObject,s3:PutObject. - EKS Full Access (Create Cluster): Required when creating new clusters from the platform. Recommended policies:
AmazonEKSClusterPolicy,AmazonEKSServicePolicy, orAdministratorAccess(recommended for initial setup). - EKS Maintenance Access (Import Cluster): Required when importing an existing cluster. Permissions: Node group access, cluster read/write operations, networking updates.
Best practices
- Create a separate AWS sub-account for Simplismart.
- Avoid using root credentials.
- Use role-based access where possible.
AWS Credentials JSON Example
Container Registries
Secrets for container registries enable Simplismart to pull private container images for your deployments and model serving. Each registry type has specific credential requirements.- Docker Hub
- Depot
- NVIDIA NIM
Docker Hub secrets are used to pull private container images from Docker Hub repositories. Use a Personal Access Token instead of your password for authentication.
Set up a personal access token
- Log in to Docker Hub.
- Go to Account Settings → Security.
- Create a new Access Token.
- Copy the token.
- Add it as a secret in Simplismart.
Best practices
- Create a separate registry or organisation for Simplismart.
- Use read-only tokens where possible.
Docker Hub Credentials JSON Example
Model Sources
Secrets for model sources allow Simplismart to access and download private or gated models from external platforms.- Hugging Face
- GitHub (Coming Soon)
Hugging Face secrets enable the download of private or gated models from the Hugging Face Hub. A Personal Access Token is required for authentication.
Set up an API key
- Log in to Hugging Face.
- Go to Settings → Access Tokens.
- Create a new token.
- Copy the token.
- Add it as a secret in Simplismart.
Best practices
- Create a separate account for Simplismart.
- Use tokens with read-only access.
- Grant access only to required models.
Hugging Face Credentials JSON Example
Kubernetes Cluster Credentials
Kubernetes cluster credentials store the necessary authentication details to connect Simplismart to an existing Kubernetes cluster. These are used when importing clusters or deploying workloads to an imported cluster.Use either token-based or certificate-based authentication, not both.
- Import clusters into the platform
- Authenticate API access
- Manage deployments
- Use a dedicated cluster for Simplismart workloads.
- Avoid sharing clusters with unrelated production systems.
- Use a dedicated subdomain for the cluster.
- Token-based
- Certificate-based
To authenticate using a service account token:
Kubernetes Token JSON Example
OCI Cluster Credentials
OCI credentials enable Simplismart to securely integrate with your Oracle Cloud Infrastructure (OCI) environment. These credentials are required to import existing OCI clusters, allowing you to deploy, manage, and scale models directly on your OCI-hosted infrastructure.Simplismart supports both token-based and certificate-based authentication for OCI clusters.
- Token-based
- Certificate-based
To authenticate using an OCI token:
OCI Token JSON Example
Generic Secrets
Generic secrets provide a flexible way to securely store any custom credentials or sensitive information not covered by the specific secret types above. These can include third-party API keys, custom authentication tokens, or other environment variables.How to add a generic secret?
- Go to Integrations → Secrets.
- Click Create Secret.
- Select Generic Secret.
- Enter key-value pairs in the required JSON format.
- Save the secret.
Generic Secret JSON Example